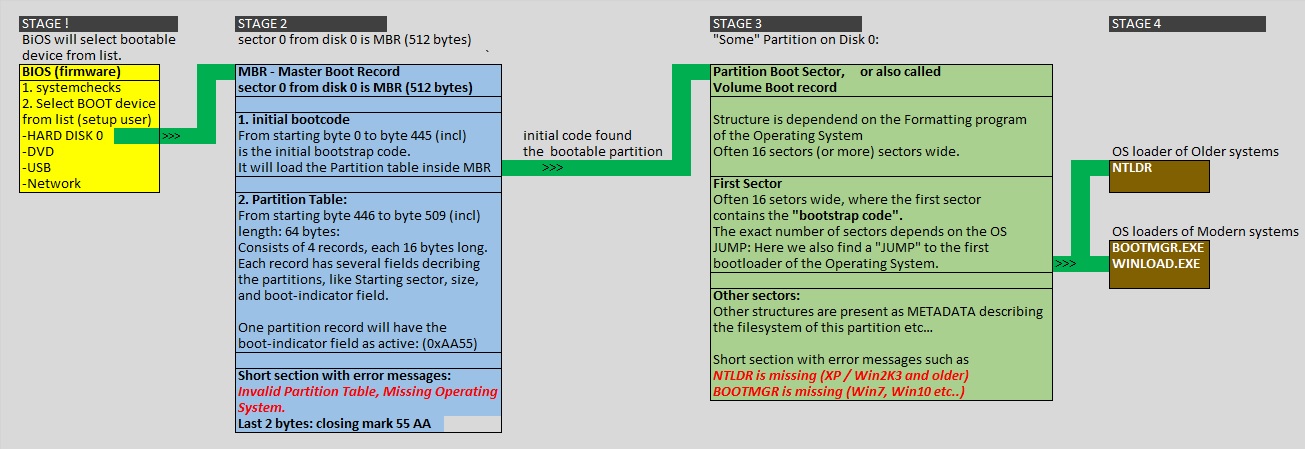
| Lengt (bytes): | Content: |
| 1 | Boot Indicator (80h=active): |
| 3 | Starting CSH |
| 1 | Partition Type Descriptor |
| 3 | Ending CSH |
| 4 | Starting Sector |
| 4 | Partition size (Sectors) |
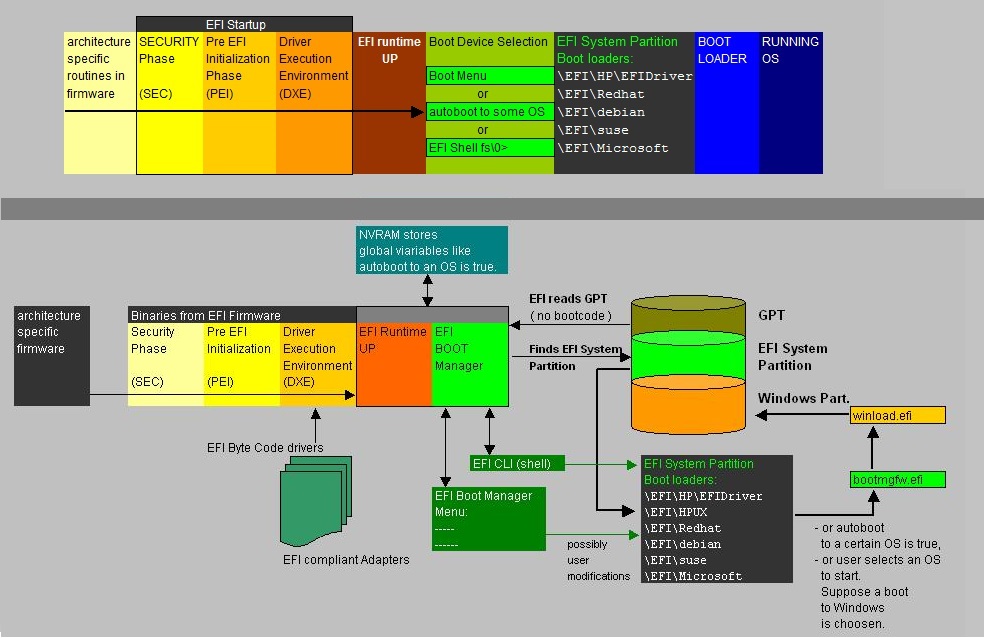
| Tool | Environment: |
| bootsect | BIOS/MBR/VBR |
| bcdboot | UEFI or BIOS/MBR/VBR |
| bootrec | UEFI or BIOS/MBR/VBR |
| bcdedit | UEFI or BIOS/MBR/VBR |
| sfc | Just a filechecker. |